Introduction
Digitalization is accelerating across all business and life aspects. Nowadays, most organizations and individuals’ daily digital interactions are happening in what is known as cyberspace or the internet. Organizations of all sizes and across industries are moving their workload to the cloud to facilitate digital transformation and enhance work efficiencies. Cloud computing is the practice of using remote computers that are hosted on the internet and includes various models such as SaaS, PaaS, and IaaS. All these models have become the backbone organizations leverage to facilitate their interactions with customers and business partners. According to Globenewswire, the global cloud computing market is expected to surpass USD 1025.7 Bn by 2028.
The cloud shift has witnessed a tremendous boost during the previous two years, especially after the COVID-19 pandemic, which forced organizations worldwide to adopt the remote working model. The new working model requires employees to access corporate resources (both data and apps) stored on cloud servers. Accessing sensitive work resources through the internet will make them susceptible to cybersecurity threats. This article will discuss major cloud threats and suggest the best prevention methods.
Cloud Computing Threats
The vast adoption of cloud computing has increased organizations’ cyberattack surface and made them vulnerable to various cyber threats.
Misconfiguration
A major reason for data breaches in the cloud is resulted by misconfiguration issues. As we know, security in the cloud is a shared responsibility between cloud customers and cloud providers. Cloud customers may not be familiar with the cloud infrastructure enough, so they make many errors when configuring their cloud infrastructure to work with their IT solutions. These errors open the door wide for threat actors to exploit for malicious purposes.
The USA National Security Agency (NSA) considers cloud misconfiguration issues a major vulnerability in cloud environments that could be prevented by:
- Designing proper cloud security policies
- Creating tight controls to protect cloud assets
- Understanding the underlying IT infrastructure of the cloud provider and ensuring local systems are integrated securely with cloud resources
Insecure APIs
Cloud applications have become commonplace these days, and many of these apps are designed using a microservices approach. In the microservice design architecture, each app is composed of different software components that interact with each other to provide a single functionality. APIs facilitate data communications between different parts when using cloud apps and accessing some cloud storage services. By using APIs, software developers can borrow functionalities’ from other software solutions without adding any code, which speeds up the entire software development process.
Failing to design and configure cloud APIs securely can make them a source of threat. For instance, threat actors can exploit poorly designed APIs to steal sensitive data or to introduce malware, such as ransomware, to the system.
Stolen Cloud Accounts
Moving to the cloud will entitle creating one or more cloud accounts for each user. Large-scale organizations need to handle a large number of users accounts, which include:
- Their employees
- Third-party providers
- Contractors and sub-contractors
- Other systems and devices – such as Internet of Things (IoT) devices
- Customers
Compromising cloud users’ accounts is dangerous, especially if the targeted account has administrative access to sensitive IT systems and data. Threat actors leverage various attack techniques, such as phishing and malware (keyloggers and spyware), to steal users’ credentials. They use their stolen credentials to exfiltrate data or to plant malware in targeted systems.
Insider Threats
An insider threat is defined as any security risks originating from within the organization, such as current or previous employees, contractors, third-party providers, and any user who has access to IT systems and sensitive data. It is worth noting that not all insider threats are malicious. For instance, negligence and lack of cybersecurity training may compromise sensitive data. For example, the unaware employee may share cloud files wrongly with unintended recipients.
Malicious insiders are dangerous because they have legitimate access to cloud resources and use their legal access to steal data and/or install malware. Various security measures can be implemented to prevent insider threats, as we will see later.
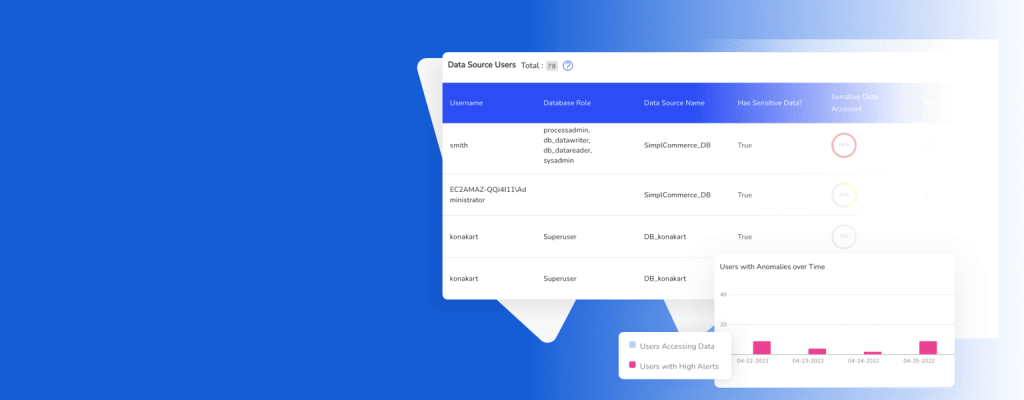
Lack Of Visibility In The Cloud
Lack of visibility remains a major issue in the cloud. The primary concern for organizations adopting cloud computing is the lack of visibility of users, applications, and network traffic when working in cloud environments. Although there are different cloud solutions to overcome this obstacle of lack of visibility, however, they remain uncomprehensive when your organization’s IT infrastructure span across different locations (on-premise and public cloud).
The lack of cloud visibility poses several performance and security issues. For instance, threat actors may compromise one endpoint device and move laterally across the target environment to steal data or plant ransomware. In the cloud, it is too difficult to monitor all digital interactions, and threat actors can exploit this to conceal their presence and conduct various malicious actions.
Data Security In Cloud
Cloud adoption brings numerous advantages to organizations; however, they should plan their cloud shift and prepare the required security measures to ensure the security of their data and applications.
Data Classification
We cannot protect data if we do not know about their existence! As most organizations’ data become digital, implementing a kind of data classification is vital to ensure that sensitive data is protected using the best security measures.
Data classification allows your organizations to classify their data according to their importance or sensitivity level. For instance, customers’ data, trade secrets, and commercial source code should be protected using the most robust security controls.
Learn how DruvStar DataVision™ provides a comprehensive data security map and data classification.
Identity and Access Management (IAM)
Leveraging the IAM solution will allow your organization to keep the credentials of all entities accessing its IT resources in one central location. For instance, entities include users, applications, systems, processes, and services. Users include employees, customers, third-party providers, and any users who access privileged organization resources.
IAM keeps all entities along with associated access permission. For example, we can define within IAM which applications and data are allowed for a particular user to access and for which amount of time. This allows your organization to give only the required access to each entity based on their job rule and nothing else.
Regulatory compliance standards, such as GDPR, PCI DSS, and HIPAA, require strong security controls to store customers’ data. Using an IAM solution increases your ability to comply with these regulations significantly.
IAM is also used to enforce IT security policies. For example, password change period, password complexity, and password renewal policy.
Backup Data
Accidents are unavoidable in IT environments, especially when your data is sent outside your organization’s data centers. Despite all organizational controls, policies, and security solutions, your cloud data could be damaged in one way or another. For instance, data loss can happen due to misconfiguration errors in some IT components. Natural disasters such as floods, fires, and earthquakes can destroy cloud data centers and prevent access to essential cloud assets. A ransomware attack could scramble all your data and make them unreadable. All these problems can happen at any time and on a large scale. Keeping a copy of your sensitive data in a safe location, preferably offline, is critical to restoring your work as soon as possible after a data loss problem.
Encrypt Cloud Data
As a rule of thumb, anything online should be encrypted first! This includes data stored at rest in cloud storage servers, data in transit between on-premise and cloud infrastructure, and all sensitive data proceed in using cloud applications.
Other Considerations (IT security policy, Passwordless Authentication)
There are other considerations for ensuring security in the cloud. The most prominent ones are:
- IT security policy: This policy indicates the accepted behavior of employees when using organization endpoint devices and when they access cloud resources – both applications and data. It is beneficial to have a dedicated policy for cloud usage which include:
- Remote access policy
- Password policy
- Incident Response policy
- Cloud backup policy
- Confidential Data policy
- Third-Party access policy
- VPN usage policy
- Two Factor Authentication: Password-only systems are subject to numerous cyber-attacks, such as credential stuffing, brute force, password spraying, and dictionary attacks. Such attacks are possible because they rely on one authentication factor to authenticate users. When securing cloud accounts, employing at least two-factor authentications, such as a traditional password and a one-time password sent via SMS or email, is critical. Passwordless authentication is also gaining popularity. This scheme works by utilizing biometric or other authentication elements that do not include using traditional passwords or motorized secrets.
Conclusion
Cloud security involves all security procedures, access controls, and security solutions used to protect cloud resources from unauthorized access. Keeping data secure in a cloud environment has become a top priority for IT leaders worldwide because of its importance to the entire organization’s work.
Remember when you use a public cloud service, such as those offered by Amazon or Google, you are putting part of your data in the hands of a third-party provider. Make sure you understand your obligations to keep your cloud data secure and your cloud provider duties in this area as well.
This article discussed the main threats organizations are expected to face when migrating to the cloud and suggested different measures to counter these threats.
If your organization operates or plans to shift to the cloud and you want to ensure you are securing your assets along the way, DruvStar offers services, such as penetration testing, vulnerability assessment, or 24/7 managed security solutions like DruvStar ThreatInsightsTM. DruvStar services cover on-prem, cloud, and hybrid environments. No matter where you are in your cloud adoption, DruvStar can help you mitigate the risks of cyber attacks and close vulnerability gaps to make your cloud environment secure.
Contact our team today to learn more about DruvStar’s services and how they can help protect your company’s assets.