Viral Patel
- June 13, 2024

Enhancing Indian Head Casino’s Data Security and Threat Detection with DruvStar’s DataVision
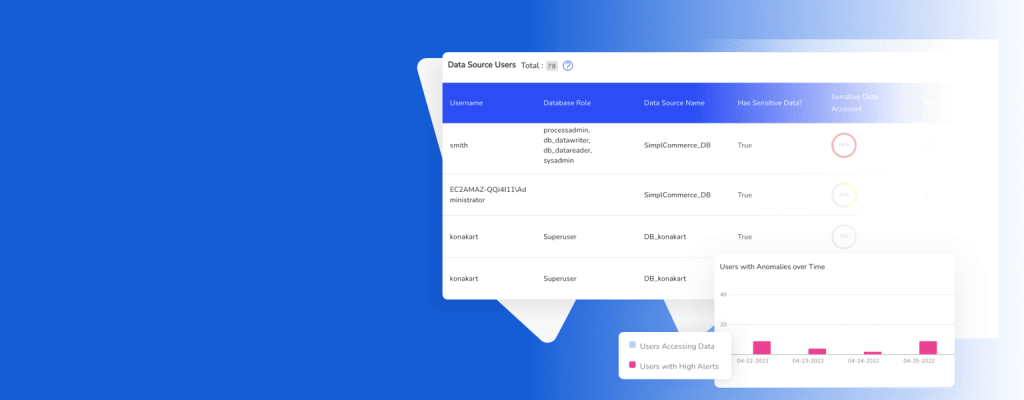
Leveraging the sophisticated anomaly detection feature of DataVision, the casino could effectively identify sensitive irregularities, significantly strengthening their threat detection capabilities.