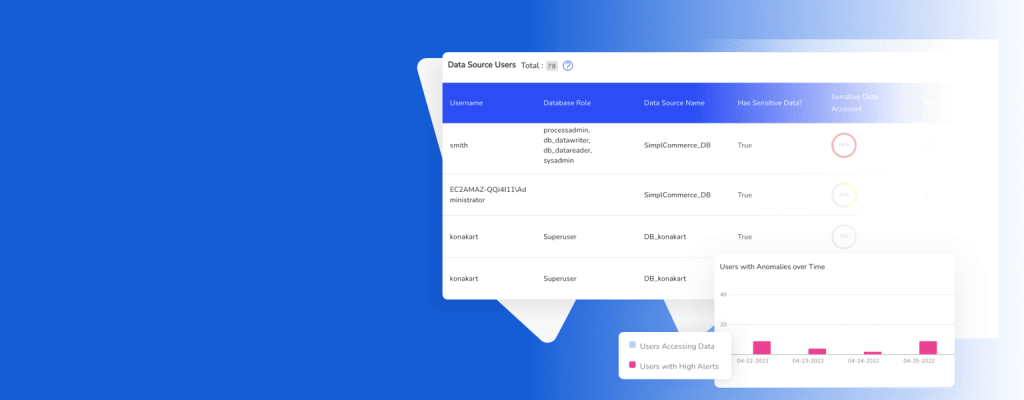
Attaining comprehensive data visibility is mission-critical if organizations want to secure their most sensitive data, consistently apply data governance policies, and comply with regulations. Several factors combine to hamper data visibility in today’s IT landscape:
- Large volumes of data move across systems with high speed and frequency.
- Data gets stored in disparate locations across a distributed environment and in many different formats.
- There are many different data sources, and sensitive data is often duplicated across different sources.
- Regulatory oversight pertaining to specific types of data can confuse organizations about what controls to put in place and in what context.
Download the whitepaper to find out:
- Why data visibility is getting harder?
- The risks of insufficient data visibility
- 4 steps to close your data visibility gaps.
- What to look for in a comprehensive data visibility solution