Introduction
The early 2000s marked the beginning of the never-ending digital era and new technologies continue to emerge on a daily basis. Intelligent technologies, ranging from artificial intelligence (AI) and machine learning (ML) to the Internet of Things (IoT) and robotics, have the power to change how we do business. In fact, they impact the way we live our daily lives. Because of their vast reach, it seems obvious that these technologies would be implemented anywhere and everywhere, and they have been.
Businesses, no matter the size, have been told that digital transformation is imperative to their success, but many are unsure of what digital transformation actually is and the wide array of effects it could have on a company. This article will define “Digital Transformation” and explore the types of threats enterprises should expect when working in the digital sphere.
What is Digital Transformation?
Digital transformation can be defined as integrating digital technologies into all business aspects. For instance, computing technologies are now used to support the core business processes of enterprises such as production, vendor relations, sales, marketing, and customer service.
The benefits of digital transformation vary, but include improved effiency, enhanced customer experiences and informed decision-making. Digital transformation also helps drive innovation, supports growth strategies, and fosters resistance to disruption in modern businesses.
While digital transformation provides numerous benefits to enterprises, it also expands their cyber attack surface and makes them more vulnerable to cyber threats. The following section will discuss the primary cyber threats IT leaders should expect when leveraging digital technologies in their work.
Cyberthreats Associated with Digital Transformation Adoption
Cloud Threats
Cloud adoption is rising across all industries and has experienced a tremendous boost since the start of the COVID-19 pandemic. Enterprises can use different cloud computing models to support their work. The most common include:
- Infrastructure as a Service (IaaS)
- Platform as a Service (PaaS)
- Software as a Service (SaaS)
O’Reilly’s 2021 Cloud Adoption Survey found that 90% of enterprises worldwide use cloud computing. Roughly half of respondendts (48%) also said they planned to migrate 50% of their applications to the cloud in the coming year. Moving data and applications to the cloud will provide numerous benefits for organizations, including:
- Cost savings for hardware/software purchases
- Facilitation of the remote-working model
- Increased competitive advantages
However, cloud benefits come with a heavy price; security!
Shifting data and applications to the cloud will introduce various security threats, such as:
- Risk of data breaches – when moving sensitive business files to the cloud, they become subject to all types of internet threats. The threat of compromising sensitive information increases in cloud environments.
- Insider threats – threats from within an organization can be either malicious or unintentional. For example, an unawere employee may share sensitive business files with the wrong recipients due to the ease of sharing files in the cloud.
- Denial of service (DoS) attacks – threat actors will try to prevent legitimate users from accessing cloud assets through DoS and distributed denial-of-service (DDoS) attacks.
- Insecure APIs – APIs are used widely in cloud environments to facilitate interactions between the cloud apps, systems, and services. Incorrectly configuring APIs increases the chances of exploitation and leave cloud apps and data vulnerable to cyberattacks.
- Account hacking – as more employees access cloud resources to do their daily jobs, the risks of their cloud accounts becoming compromised increases and they are more susceptible to different cyberattacks, such as phishing and malware attacks.
- Misconfiguration errors – Cloud systems are scattered across different geographical locations which can make them difficult to protect. The security of the cloud is the shared responsibility of the vendor and the cloud customer. Cloud customers may not have the required technical expertise to configure cloud IT infrastructure correctly and share their cloud data securely with other external parties.
Supply Chain and Third-Party Risks
Today’s business environments are interconnected across the globe. Many organizations choose to outsource part of their service to third-party providers. To ensure smooth collaborations, enterprises need to give access to their confidential data and systems to external providers, such as contractors, sub-contractors, third-party providers, and other vendors that provide particular services/products. In most cases, external parties do not have the same security measures and access controls as the enterprise they are serving. A vulnerability with third-party vendors could compromise the data and apps of their clients. Threat actors know this fact very well and are now targeting external parties to have an entry point to the target enterprise’s IT environment. The attack against SolarWinds, a major cybersecurity firm, is an example of exploiting a third-party supply chain to gain entry into the target enterprise’s IT environment.
Remote Working Threats
Since the pandemic, the remote working model became widespread, impacting businesses worldwide. Even after the pandemic fades, the remote working model will remain prevalent and may even increase. According to Foundry’s 2022 Future of Work Study, 71% of respondents expect their workforce to be hybrid or remote only for the foreseeable future.
Remote working provides many benefits, such as increasing employee productivity/performance and saving enterprise costs. However, remote working does require employees to access their corporate resources via the internet, and this exposes them to cybersecurity risks originating from the internet.
Many enterprises chose to rapidly adopt the remote-working model in 2020 without considering the security implications. Cybercriminals exploited this to use the many security gaps of not implementing the best security practices when working remotely.
Compliance Challenges
Another challenge of the digital transformation revolution is the legal and compliance side. For instance, third-party vendors could be located in different countries, each subject to different national data protection regulations. Digital transformation requires having a strong online presence to deliver services and products across the globe.
The open nature of online business introduces further legal complexities when dealing with customers located in different countries. For example, any company dealing with EU customers should adhere to the GDPR regulation when collecting, maintaining or storing the personal and financial information of customers. Additionally, some industries have specific regulatory compliance standards that must be met, such as PCI DSS, and HIPAA. Managing third-party compliance issues is complex in the digital world, especially for large scale companies.
Mitigating Security Challenges Caused by Digital Transformation
Become Proactive
Becoming proactive in the cyber world is the best solution to prevent sophisticated cyberattacks against your IT infrastructure. The traditional approach to handling cybersecurity is calling your managed IT services provider (MSP) or the internal IT security team when a cyber incident occurs. This is no longer enough because cyberattacks can cause wide work disruption and waiting for them to occur and cause harm to the business is not ideal. Instead, proactive cybersecurity will work to prevent cyber incidents before they happen. For example, by using cyber threat intelligence feeds from external providers, businesses can discover security vulnerabilities in their IT environment and work to fix them before they cause problems to normal operations.
Managing third-party risks
It is better to classify third-party providers into risk categories according to their:
- Service type
- Location
- Governance and compliance standards
Businesses should conduct regular audits of their third-party partners to ensure:
- They have implemented the required cybersecurity defense plan to protect their assets.
- They have installed proper security solutions, such as NDR, SIEM, Firewalls, and IDS/IPS.
- Their employees follow proper cybersecurity awareness training programs to recognize social engineering and other cyber-attack types.
- Their data breach notification requirement meets your regulatory compliance needs – for example, if they suffer from a data breach, they should inform you within an acceptable period.
Remote employee safety tips
There are different measures enterprises can take to secure their remote workforce:
- Install a comprehensive antivirus suite that can prevent viruses, spyware, spam, and malware.
- If possible, try to give your employees laptops to do their work at home. This allows your enterprise to secure employee devices using the same measures used in the work environment.
- A reliable VPN solution should secure all employees’ connections to corporate resources.
- Ensure all employee devices operating systems, and applications are current.
- Use a centralized storage solution so your employees will not need to store business-related files on their personal devices. Utilizing cloud storage for this task is an option.
- Protect your online meetings with strong passwords when using Zoom or other virtual meetings platforms.
- Request that your employees secure their work accounts and personal computing devices using strong and complex passwords. Employing two-factor authentication and passwordless authentication will enhance their protection.
- Provide guides and best practices for your employees to secure their home Wi-Fi networks.
Staying In Compliance During Digital Transformation
Big enterprises have dedicated compliance offices to handle compliance issues, however, small enterprises who cannot afford the cost of having such capabilities find it beneficial to hire legal counsel for advice when digitally transforming their services and entering new markets.
There are several different areas of compliance companies should be aware of inlcuding:
- Licenses, and recertifications
- Internal work operations
- Ongoing filling requirements (which could be suddenly imposed by government or international regulators)
Taxes are another area of compliance that businesses need to be concerned with. Many small and medium-sized companies are now using automated solutions to calculate their tax requirements. TurboTax is an American company that provides the service of preparing American income tax returns. Other services exist to outsource automating taxation and IT service needs.
Conclusion and A Future Outlook
Digital technologies have become widely used in organizations of all sizes and across all industries. Transforming your current business processes digitally brings numerous benefits, however, it also increases the potential for cyberattacks against IT infrastructure and makes them subject to different cyber threats.
This article discussed the main challenges organizations face when they apply digital transformation and suggested different countermeasures to make the digital shift more secure and organized.
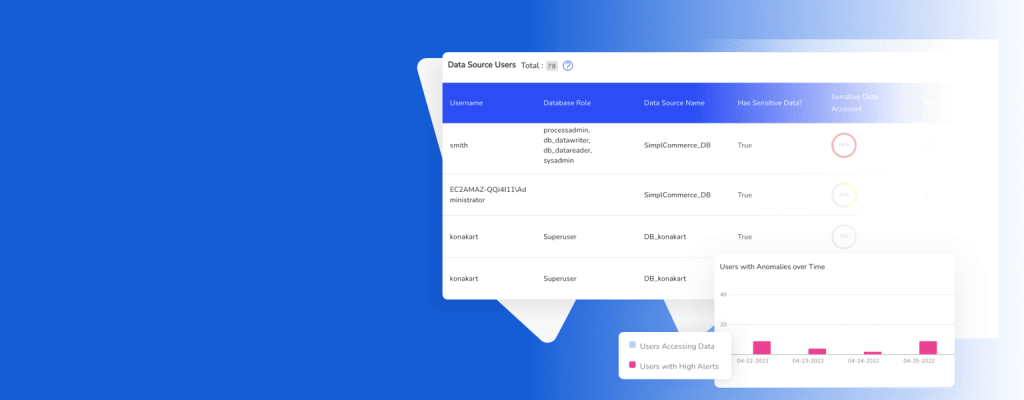
If your organization is undergoing digital transformation and you want to ensure you are securing your assets along the way, DruvStar’s offers services to assist with the transition such as penetration testing or more long-term security solutions like Managed Detection and Response (MDR). No matter where you are in your cybersecurity journey or digital transformation implementation, DruvStar can help you mitigate the risks of cyber attacks and close vulnerability gaps.
Contact our team today to learn more about DruvStar’s services and how they can help protect your company’s assets.