In today’s digital age, having secure software is essential for protecting digital assets, including customer data, which is often the most critical asset an organization has.
Organizations must develop software products quickly in a rapidly changing environment. To ensure their final product is secure and minimize testing time, they should use various tools and processes throughout the software development life cycle.
Security testing evaluates your software product against a wide range of security risks to identify and fix any vulnerabilities before releasing it to the market. Many applications today are cloud-native, interacting with backend servers and networks to complete their tasks. This opens the door for malicious actors to exploit any vulnerabilities to gain unauthorized access to your IT environment.
In this article, we outline steps your company should take to ensure its software is secure before releasing it to production.
Secure architecture review
We first need to conduct a comprehensive software architecture review of the surface area which is vulnerable to cyber-attacks. This review is essential in order to identify any security weaknesses in the current application design, and then use those findings to re-architect the design for the purpose of reducing or eliminating any potential attack surfaces that malicious actors could exploit. Through the review, we can ensure that the application is designed and built with the utmost security in mind, so that it is able to protect itself from potential cyber threats. By taking all of these steps, we can create an application that is secure and robust enough to withstand any malicious attempts to gain access.
OWASP Top 10 training
The OWASP Top 10 is an invaluable resource for web application developers, providing a widely accepted standard and framework for assessing the security of their applications. With this framework, developers gain an understanding of the various threats that their applications may be exposed to and can then take the appropriate measures to mitigate them. It is essential that your developers are well-trained in using the OWASP Top 10, as they will be able to identify potential threats and vulnerabilities, and develop strategies to safeguard against them. Furthermore, utilizing the OWASP Top 10 will ensure that your applications are up to the highest security standards.
Contact DruvStar if you would like your developers to be trained in OWASP Top 10.
Document non-functional security requirements
The non-functional security requirements are a vital component of any system, and encompass how the system performs in a specific function. This includes the ability to audit the system for any user abuse, which is an important security requirement. For example, keeping accurate audit records of user access to the system is a non-functional security requirement that may be critical for the functioning of the system. These records are important for providing an account of system activity and can be used to detect any potential malicious activity. Additionally, audit records can also be used to track user access to the system and ensure that only authorized personnel are accessing the system. As such, audit records are an important non-functional security requirement that can be used to ensure the security of a system.
Secure against SQL injection attacks
This is one of the most dangerous attack against web applications. SQL injection attack works by inserting malicious SQL statements into a web application form, such as a login or search form, to query the backend database and retrieve sensitive information.
Attackers leverage automated tools like SQL Map, SQL Ninja to speed up the process of discovering and exploiting SQL flaws. Developers should be aware of these techniques and consider SQL injection when developing and testing web applications. The most important countermeasures against this type of attack are:
- Performing input validation on all users’ entered data
- Disabling database errors from appearing in the web application
- Using safe programming functions in prepared statements and stored procedures
Validate input data
Adversaries exploit applications by supplying malicious input to make them behave differently than their developers intended. For instance, any data entered into the application should be properly formed and not stored in the database while it is malformed. The priority remains for all data coming from outside your organization (such as your customers and app users), however, internal data provided by your employees should be validated as well. If your application validates your data on the client side, you should also consider validating it again on the server side for additional layer of security.
Enforce proper access control
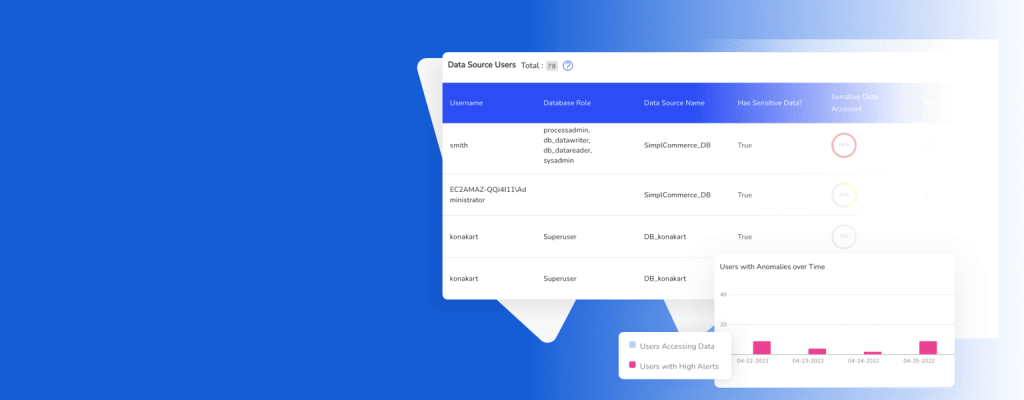
Deciding who has access to each portion of your data should be planned early in the design process. The access control rules should be centralized in your IT environment, so you can audit user access and update users’ access rules centrally.
It is advisable to make access decisions in your system depending on server-side data and not on client-side data. Besides, it is better to use the “default deny access rule” which means no one can grant access to the protected resources unless authorization is established to perform the specific action.
Identity management
Creating a system that manages user identities and sessions from ground up is not easy. You can use many out-of-box identity management solutions that facilitate this function.
If your application still accepts user signing using traditional passwords, then make sure to request strong and complex passwords from users. Passwords should be hashed or salted before storing them in the backend database. OWASP provides a cheat sheet for best practices when storing password hashes.
Enabling Two-Factor Authentication (2FA) and Multi-Factor Authentication is better for protecting and accessing sensitive resources. Passwordless Authentication that leverages no passwords (e.g., biometric, magic links, software, and hardware tokens) is a modern scheme that has become increasingly used by web applications.
Protect data using encryption
When user data is processed by your application, data should be encrypted in its three states: At transit, at rest, and during processing.
OWASP provides a guide on implementing transport layer protection for an application using Transport Layer Security (TLS). Developers should note the following things in advance:
- It is better not to use in-house encryption algorithms. Using foolproof and mature encryption libraries is better than developing an internal encryption scheme. OWASP provides a guide on best practices when implementing encryption at rest.
- All data processed or transmitted via your application should be encrypted.
- Key management is essential to keep the entire encryption process secure.
Enable appropriate logging
The ability to log different events types in applications is critical for more than one area, for instance:
- Logging allows the security team to track intrusion attempts and know when a specific intrusion happened.
- Logging is critical for digital forensics. It allows inspectors to investigate data breaches and collect vital information about an attack.
- Logging allows system and network administrators to troubleshoot specific problems, such as performance issues, and solve them.
- Logging allows internal policy violation monitoring and provides a baseline for recording normal behaviors of users and applications when using IT systems.
Application developers should consider creating a unified logging mechanism for their applications that can be consumed by various systems and applications across their IT environment. This makes the process of correlation and analyzing events easier.
Keep in mind that logging should be informational and helpful; however, it should not be designed in a way that leaks the organization’s confidential information.
Perform an assessment of third-party code
Most applications will require using source code from external libraries. When it comes to security, it is better to use well-known libraries maintained by commercial companies or with broad support from developers.
Development libraries such as Spring Security, Ruby on Rails and .NET come with rich and extensive security features. Developers should train on using their features and know how to implement them properly in their applications.
It is critical to keep your code up to date when using open source code libraries. It is usual for open-source code to suffer from security vulnerabilities, however, keeping it current should mitigate such problems. OWASP has developed a great tool called OWASP Dependency-Check which helps software developers detect publicly disclosed security vulnerabilities within a project’s dependencies and patch them accordingly.
Handle errors and exceptions correctly
Improper handling of errors in your application code can lead to serious security risks. For instance, if a developer forgets to handle an error or exception, attackers could exploit it to gain unauthorized access. On the other hand, the developer should ensure any unexpected error will not leak sensitive information about their application or website.
A common error when designing a login page is specifying the error message to the user. For example, “the entered username is wrong” or “password is incorrect”. A good design should state that “either username or password is incorrect” which does not reveal much information for the attacker to guess which field is entered incorrectly.
Incorporate security testing
Security testing should be integrated into the software development life cycle. Testing uncovers security vulnerabilities and design flaws in applications and helps developers fix them before they get exploited by attackers.
There are mainly two types of security testing:
- Static analysis: In this testing type, the application is tested from the inside out without executing the program, hence, why it is called static. The application code is examined thoroughly for any flaws in design or insecure libraries that can lead to a security problem.
- Dynamic analysis: In this type, the application is tested at run-time or during program execution. It looks at the application from outside while running and tries to discover any security vulnerability. Tester uses the same attack techniques leveraged by hackers to see how the application behaves under attack.
Continuous monitoring
After taking all the necessary steps to secure our applications, it is important to remember that monitoring for security threats should be an ongoing process. This should be done not only in production environments, but also in development and test environments. Ensuring your applications remain safe requires you to consistently monitor these environments for potential security risks. Continuous monitoring enables you to detect potential issues quickly and address them before they cause any significant harm.This is a crucial step in ensuring the ongoing safety of our applications and should not be overlooked.

Summary
The document outlines a comprehensive security process that should be implemented before releasing a product to ensure its safety and reliability. The process consists of a series of steps, including evaluating the product’s security requirements, identifying potential security threats and vulnerabilities, creating a security plan, testing the product to verify that the security plan is effective, and implementing any necessary corrective measures. The process also involves monitoring the product’s security over time to ensure that it remains secure.
If your organization operates or plans to shift to the cloud and you want to ensure you are securing your assets along the way, DruvStar offers services, such as penetration testing, vulnerability assessment, or 24/7 managed security solutions like DruvStar ThreatInsightsTM. DruvStar services cover on-prem, cloud, and hybrid environments. No matter where you are in your cloud adoption, DruvStar can help you mitigate the risks of cyber attacks and close vulnerability gaps to make your cloud environment secure.
Contact our team today to learn more about DruvStar’s services and how they can help protect your company’s assets.