In this ebook we cover:
- Introduction
- Objective of Cyber Attack Emulation
- It differs from traditional security testing methods
- Implementing Cyber Attack Emulation
- Emulation of Adversary Attack Pattern
- Timelines
- Outcome
- Lessons Learned


In this ebook we cover:



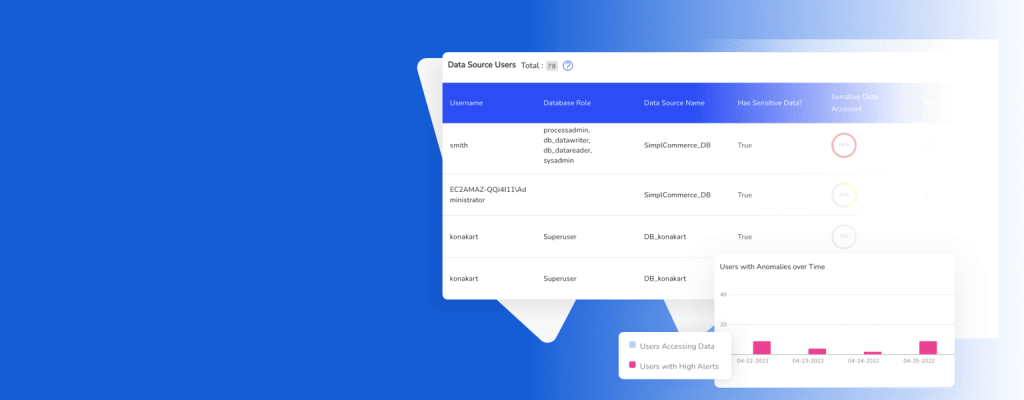

DruvStar cybersecurity, your trusted partner. Using a combination of in-house expertise and industry partnerships, we deliver modern security solutions at scale to strengthen your infrastructure.

DruvStar 6671 South Las Vegas Blvd,
#210 Las Vegas, Nevada , 89119
702-761-6814