Vulnerability scanning and penetration testing are two activities commonly used to identify weaknesses in servers, operating systems, application services, and network devices that attackers can exploit. The two activities are related, but they are not the same. This article clarifies the main differences between vulnerability scanning and penetration testing.
The Current Vulnerability Landscape
The number of vulnerabilities found in production code and recorded in the US-CERT Vulnerability Database reached a record high of 18,335 in 2020. This was the fourth year in a row that record levels of vulnerabilities were reported.
Examples of vulnerabilities include badly configured network firewalls, application logic flaws, and inadequate endpoint security. Given the number of vulnerabilities and the high costs of an information security breach, efforts to proactively find and fix network security weaknesses are fundamental in improving your cybersecurity defenses.
What Does a Vulnerability Scan Do?
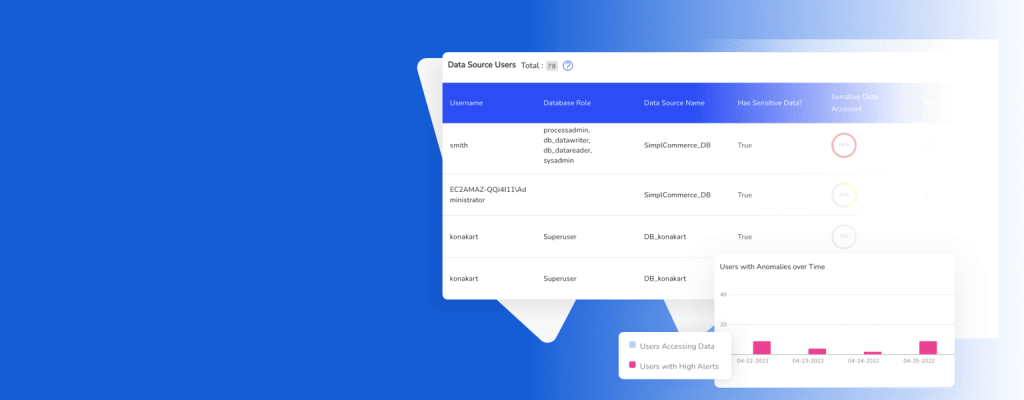
Vulnerability scanning uses tools to look for known vulnerabilities in your network, systems, and applications. The tools used for vulnerability scanning perform automated searches for vulnerabilities, which means quick wins in terms of identifying weaknesses you can address within your IT infrastructure.
Vulnerability scans report on the vulnerabilities identified and their severity levels. The scanning tools use databases of known vulnerabilities, such as the CVE security vulnerability database. The tool takes an inventory of your network assets, operating systems, installed software, and open ports and tries to detect weaknesses by cross-checking your systems with their databases.
What is Penetration Testing?
Penetration testing simulates genuine cyber attacks by tasking an individual or group of security professionals with ethically detecting and exploiting vulnerabilities within your IT infrastructure. Penetration testers use knowledge across several domains, tools, technical skills, and security protocols to gain access to your systems and sensitive data.
The three broad types of penetration tests are:
- Black box tests: you don’t provide any information about your IT environment to the tester.
- White box tests: you provide the testing team with complete details about your network, systems, and applications.
- Grey box tests: you provide some limited information about your environment, such as the IP addresses of target systems.
What is the difference between penetration testing and vulnerability scanning?
Before getting into the key differences between vulnerability scanning and penetration testing, it’s important to clarify some terminology:
- Vulnerability management is an ongoing process involving identifying, classifying, mitigating, and remediating cybersecurity weaknesses over the long term.
- A vulnerability assessment is a systematic way of identifying, categorizing, and reporting on cybersecurity weaknesses, and it is conducted within a specific timeframe.
Purpose
Both vulnerability scanning and penetration testing have a similar high-level purpose, which is to help an organization with its vulnerability management. Both activities commonly feature in vulnerability assessments.
The difference in purpose is best understood in terms of the scope of these activities. Penetration tests are far broader in scope; they encompass both looking for vulnerabilities and actually exploiting them as a malicious intruder would. Penetration tests are good indicators of the maturity of an organization’s information security strategy.
If a vulnerability scan is equivalent to a friend checking if your car is secure and letting you know if you have any unlocked doors or windows, a penetration test would mean your friend breaks into your car via an unsecured door or window and trying to start the engine.
Duration
- Vulnerability scans: Because of their high levels of automation, vulnerability scans typically take anywhere from a few minutes to a few hours to complete.
- Penetration tests: Because of their reliance on human expertise, penetration tests can range in length from a few days to a few weeks.
False Positives
Vulnerability scans are far more susceptible to problems with false positives; i.e. threats that aren’t real. The reason is that vulnerability scanning tools depend heavily on the availability of all relevant information, including configuration details.
Sometimes, the tool can’t authenticate on the endpoint, which limits the information that can help determine whether vulnerabilities are actually present. The level of human input and involvement in penetration tests limits false positives to a far lower level than vulnerability scans.
Level of Automation
- Vulnerability scans have high levels of automation. The manual input to a vulnerability scan is typically limited to scheduling ad hoc or regular scans to run and reading reports after the scan completes.
- Penetration tests have low levels of automation because they depend on trained security professionals to run them. It’s important to note that penetration testers often use automated vulnerability scanning tools as an initial part of their testing, but manual input is a much more significant aspect.
Why Penetration Testing Is Required
Both vulnerability scans and penetration tests are required under the PCI DSS regulation, which applies to entities that store, process, and/or transmit cardholder data. However, if you don’t need to comply with PCI DSS or any other regulation that specifically mandates penetration testing, it’s natural to wonder why you need penetration testing given its complexity and duration.
The most compelling reasons to use penetration testing aside from compliance mandates are:
- Uncover unknown vulnerabilities—penetration tests are superior at finding vulnerabilities that don’t exist within databases of reported vulnerabilities. These unknown vulnerabilities can be exploited by genuine attackers to wreak havoc on systems and steal sensitive data.
- Leverage security expertise—when it comes to identifying vulnerabilities that attackers can exploit, tools are no replacement for experts with in-depth technical and security knowledge. Penetration tests typically have knowledge of SQL injection, remote access attacks, front-end technologies, networking protocols, scripting languages, and most importantly, human behavior.
- Simulate genuine cyber attacks—genuine cyber attacks are extremely dynamic and unpredictable. Penetration tests allow for rapid adjustments in response to evolving conditions within your IT environment.
DruvStar’s Penetration Testing
DruvStar offers bespoke, comprehensive penetration testing solutions. Here are some ways our services go the extra mile to help your organization find exploitable vulnerabilities:
- Multiple testing iterations: our comprehensive approach uses DevOps and Agile models to test, learn, and re-test until all risky areas of your environment are uncovered.
- Test what you want: we have bespoke offerings from external pen tests to dynamic application security testing to mobile app security testing.
- Vetted results: we vet our results for true positives so that you only spend time mitigating genuine threats.
- Remediation recommendations: get expert recommendations on the best way to remediate any vulnerabilities we find within your IT infrastructure.
Contact us today if you’d like our help in identifying and mitigating your key information security vulnerabilities.