Penetration Testing Service
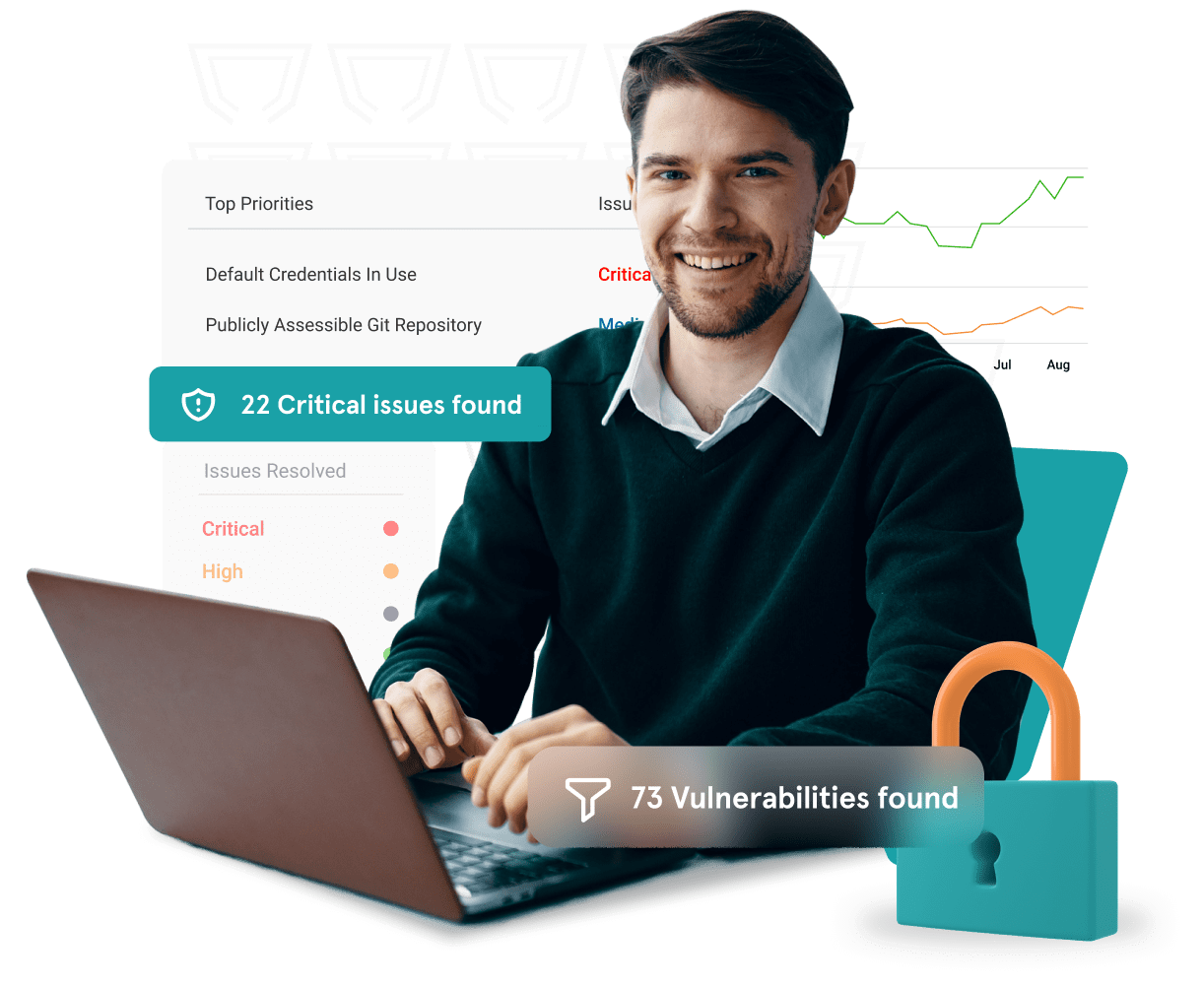
Close the vulnerabilities that attackers use to infiltrate your systems.
DruvStar’s Cybersecurity Assessment Services unpeel the cybersecurity onion, assessing every layer to uncover opportunities for attack. DruvStar works closely with your team to harden each attack vector, making your environment almost unhackable.

"We wanted somebody we could trust and rely on, which would allow us all to sleep better at night."
Penetration Testing
Are you vulnerable to being attacked from the outside? Find out with DruvStar's Penetration Testing. Get a free retest after closing your gaps.
Internal Vulnerability Scan
If an attacker should find their way in to the system, what will they find when they're there? Make sure there's nowhere for them to go and nothing that they can do from the inside.
D-SWAT
DruvStar's version of the SWAT team. An on-site engagement to root out Advanced Persistent Threats and actively hunt for bad actors in your environment. On average, one week of prep and one week with boots on the ground.
Product Security Verification
A unique DruvStar offering to ensure that your products are security-safe before being deployed to a customer's environment.
Mobile application security testing
Are you about to ship your latest mobile app on iOS or Android? Before collecting any personal or sensitive data, make sure your product is secure from mobile client to your back end services.
Web Application Security Testing
Websites and APIs, can be a feeding ground for bad activity. DruvStar's Web Application Security Testing identifies common and uncommon attack opportunities to harden your solutions.
Security Readiness Assessment
How do your policies and procedures hold up to scrutiny? Do your actual actions align to your stated goals. Let DruvStar help you get to the next level.
Coverage...
Infrastructure
- Cloud
- on-prem
- co-located
- hybrid
Endpoints
- Workstations
- Servers
- Mobile
- IoT
- Custom devices
Network
- Firewalls
- Routers
- Group policies
Engagement Models
Set a baseline for evaluating your existing systems. Align to compliance audits. Get retested once you have remediated.
As new product is released, new environments come on line, or new offices are opened.
Plan testing throughout the year to ensure ongoing verification of any changes while continually verifying against the latest security intelligence.