Covid-19 and The Current Risk Landscape
According to the 2021 Allianz Risk Barometer report, the top five risks faced by businesses in 2021 are:
- Business interruption
- Pandemic outbreak
- Cyber incidents
- Market developments
- Regulation changes
In light of the Covid-19 pandemic, it’s worth noting how the three main risks businesses face are closely intertwined. The Covid outbreak reflects a standalone pandemic risk for businesses, but its impact increases several other risk types. For example, business interruption increased to an unprecedented level as a direct result of the pandemic.
The risk of cybersecurity incidents also has a heavy link to the pandemic. Covid-19 hastened the rapid adoption of remote working, which increased the surface area for successful cyber attacks. Opportunistic lone wolf hackers and hacking groups sought to exploit the uncertainty and fear that this situation introduced.
A report by Deloitte into Covid-19 and cybersecurity found some startling statistics highlighting the impact of the pandemic on cybersecurity:
- 47% of individuals fall for phishing scams while working at home
- The proportion of unseen malware attacks grew from 20 percent before Covid to 35 percent during the pandemic
- The average cost of a data breach resulting from remote working is $137,000 in some areas
What is Cyber Risk?
Cyber risk is the likelihood of harm to an organization resulting from the loss or failure of its information assets and/or information systems. Cybersecurity risks can cause financial damage, business disruption, and reputational damage. The risks extend to harming individual employees and business partners.
A key driver of cyber risk is the strategic adoption of new types of technologies by businesses. As companies try to achieve growth and improve performance, they increasingly turn to technological options, such as cloud computing, IoT devices, remote access solutions, containers, and BYOD policies.
While technological adoption and digital transformation undoubtedly benefit businesses, they also increase cyber risks by leading to increased infrastructural complexity. The increased cyber risk is reflected in the statistics about cyber crime over time.
According to Statista, there were 157 data breaches in the United States in 2005 versus 1,001 in 2019. The number of cybersecurity incident reports by federal agencies in the United States grew from 5,503 in 2006 to 31,107 in 2018.
Types of Cyber Risks
Businesses face a plethora of both internal and external cyber risks. The obvious example of cyber risk is a malicious outsider potentially hacking an application and stealing sensitive information. However, cyber risks encompass a broader set of risks, including both unintentional and internal risks. For example, a system admin might make a misconfiguration error that exposes your company to a data breach.
Hackers deploy a range of different attack methods and techniques in an attempt to gain access to networks and steal information or to bring systems down. These attack methods include but aren’t limited to:
- Ransomware. A type of malware that encrypts victim’s information and forces them to pay ransom money in order for the data to be unlocked.
- Phishing campaigns. Phishing is a fraud tactic of pretending to be someone or something trustworthy in order to steal personal information. Cybercriminals use deceptive emails and other tactics such as phone calls and text messages, to pose as reputable companies or individuals – email scams are the most popular form of phishing.
Learn more about phishing in our free ebook.
- Distributed denial of service (DDoS). Distributed denial-of-service (DDoS) is an attack that shuts down a website or server by overloading it with more traffic than it can accommodate.
- Malware. Malware is unwanted software that installs itself on an unsuspecting target, causing unusual behavior.
- Zero-day exploits. A zero-day refers to a computer vulnerability unknown to those who should be aware of its possible implications (including the vendor). Until the vulnerability is fixed, hackers can use it to compromise programs and data. A new attack type that exploits this vulnerability—specifically targeting its existence unpatched—is called a zero-day attack or a zero-day exploit.
- SQL injections. SQL injection is a form of attack that leverages malicious SQL code to exploit vulnerabilities in the backend database and access information not intended for public consumption.
How Do You Identify Cyber Risk?
A cyber risk assessment is a structured process that identifies the information systems and assets exposed to risk, the risks involved, the likelihood of those risks occurring, and the potential severity of their impact.
Each organization faces its own set of cyber risks and needs to prioritize those risks according to their likelihood and severity. It would be unwise to purchase a new technical cybersecurity solution or implement a new security procedure without first understanding what risk you’re trying to mitigate with it. Here is an actionable step-by-step guide to carry out an effective cyber risk assessment.
Gather information about the organization’s assets and how they are used
To understand the threats facing your information assets and IT infrastructure, you must first understand what your assets are and establish a baseline about how they are being used. These assets include data, databases, servers, applications, workstations, virtual machines, cloud applications, firewalls, and more. Put a value on these assets to help understand the loss that can occur if they are stolen, damaged, or interrupted.
Identify the internal and external threats to each asset
This step is all about listing all possible threats both inside and outside the organization that have the potential to harm your information assets and systems. Threats include natural disasters, system failures, payment card skimming, human error, third-party software vendors, nation-state cyber attacks, malicious insiders, ransomware attacks, service disruptions, data breaches, and accidental data loss.
Assess your vulnerabilities
Vulnerabilities are weaknesses within your network, infrastructure, or applications that hackers can exploit. For example, not applying a security patch to an application can introduce vulnerabilities. Other vulnerabilities can include misconfigurations, authentication failures, and unintentional data exposure.
Assessing vulnerabilities provides visibility into specific weak points that increase cyber risks. Threats alone don’t always increase cyber risks because there needs to be a vulnerability for a threat to exploit.
Determine the likelihood of risks
The next step is to estimate the likelihood of specific risks so you can categorize and prioritize them. A simple and practical formula for estimating risk likelihood is:
Cyber Risk = Threat Probability x Vulnerability Exposure x Asset Value
Even though this is a formula that specifies the chances some outcome will happen, its results don’t need to be in numbers. You can qualitatively describe probabilities and risks as low, medium, or high. The point is to logically understand your risk profile based on the key determinants that impact each risk.
For example, you could determine that there’s a medium likelihood of website downtime resulting from the threat of a DDoS attack. It’s more difficult and time-consuming to calculate exact quantitative values for risks because you need to depend on a lot of historical data and statistical techniques.
Quantitative assessments are easier for management and executives to digest and communicate about. The goal here is to facilitate communication and evaluation of risks—you don’t need a precise dollar figure for this to happen.
Identify the potential impact
With a basic framework in place for understanding risks, it’s also useful to highlight the potential impact of loss, disruption, or damage to information systems and assets. For example, an hour of website downtime may cost $30,000 per hour. You can use industry studies and benchmarks to identify the potential impacts of each risk.
Some cyber risks might have a high likelihood of occurring but a low potential impact with minimal disruption to services or no loss of sensitive information. Again, you can be qualitative when identifying impact severity. Consider using a scale with values ranging from very low impact to critical impact.
Document results
A risk assessment should be documented in the form of a report that decision-makers can use to decide on the budget, controls, processes, people, and procedures necessary to manage the most pressing cyber risks. The risk assessment report can highlight risks, specify the likelihood of risks, and suggest recommendations to manage those risks.
Armed with a thorough cyber risk assessment, your organization can decide on the necessary steps to prevent, defend against, and otherwise mitigate your key cyber risks.
Tips to Reduce Risks of Cyber Attacks
The volume and complexity of cyber risks faced by organizations make estimating and calculating every single risk a difficult task. Regardless of how accurately or thoroughly you can measure risk, cyber risk management helps to reduce the probability of those risks. Here are six useful tips for effective cyber risk management:
- Create a security plan that specifies processes and procedures that can reduce the risk of data loss or theft.
- Provide employees with ongoing cybersecurity awareness and training programs to keep security front of mind and reduce the human elements of cyber risks.
- Take an inventory of all network assets, including all devices connected to the network, so that you have visibility into your cyber attack surface.
- Use tools, security experts, and technologies to identify existing vulnerabilities within your IT infrastructure.
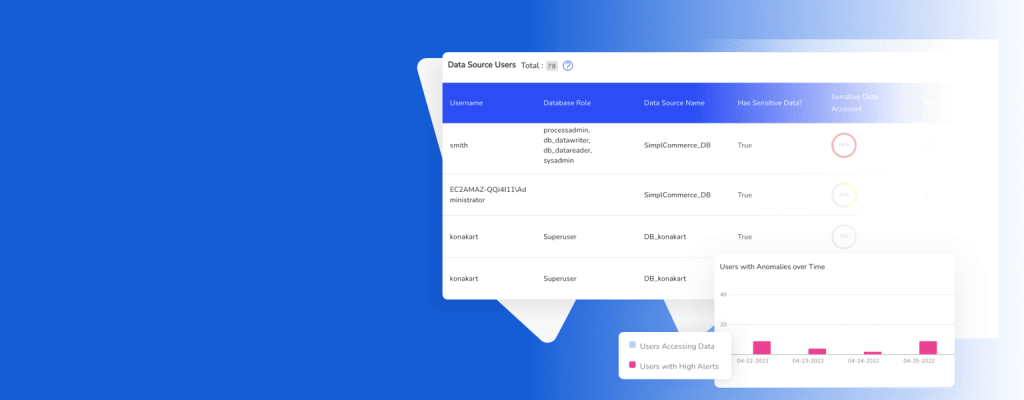
- Proactively monitor systems using in-depth detection that scans for threats both inside and outside your organization’s perimeter.
- Implement an incident response strategy to reduce the impact of any breaches of your cybersecurity defenses.
Read more: 6 Effective Ways Companies Can Avoid Becoming a Cybersecurity Victim
Wrapping Up
Cyber risk is a primary source of risk that affects every organization in every industry. The risks faced by different organizations differ, so there is no one-size-fits-all cyber risk management solution. A cyber risk assessment is vital for identifying the actual risks you face and putting in place tools, strategies, policies, and people to mitigate those risks.
A crucial aspect of effective cyber risk management is understanding the existing vulnerabilities your organization faces. It takes a multi-pronged approach and security expertise to find all existing vulnerabilities within your IT environment.
Druvstar’s Vulnerability Discovery service includes comprehensive security testing and assessments to uncover vulnerabilities that increase your exposure to cyber risk. We provide repeated, continuous, and multi-faceted security testing. Manage your organization’s cyber risks today.