Is your organization prepared for data breaches? Are you adopting government-backed approaches to cybersecurity? The zero trust model continues to gain traction as a network security best practice that helps organizations defend against data breaches. This article provides an overview of zero trust, including its growing relevance, implementation benefits, key principles, and how to enforce it with anomaly detection.
The Emergence of Zero Trust
The emergence of zero trust traces its origins to a 2014 Google security initiative known as BeyondCorp, which regarded internal networks and external networks to be completely untrusted. BeyondCorp based access policies to applications, data, and other resources on information about a device, its state, and its associated user.
Facing difficulties in protecting against data breaches in complex IT environments, organizations began to emulate the BeyondCorp strategy. A recent survey of IT decision-makers found that 72 percent of respondents plan to adopt zero trust or are in the early stages of its rollout.
Modern IT environments are distributed across hybrid on-premise data centers and cloud infrastructure. Workforces are characterized by employees working both remotely and on-site. These two factors together require an approach that protects data and other resources regardless of their location and the location of users trying to access those resources.
By providing context-aware access to sensitive data, the zero trust model can harden against unauthorized or inappropriate levels of access that lead to data breaches.
The Biden Administration’s Zero Trust Executive Order
In May 2021, the Biden administration released an Executive Order (EO) outlining how to improve the nation’s cybersecurity posture. A key recommended practice in this EO was to, “ develop a plan to implement Zero Trust Architecture.”
The 2021 EO has implications beyond the governmental level. The private sector makes up a significant proportion of organizations that ultimately collect and store sensitive data. Private sector businesses have a responsibility to protect individual privacy and secure sensitive data stored about customers, business partners, employees, and contractors. This responsibility extends to compliance with regulatory frameworks designed to further protect individual data privacy.
What Is Zero Trust Security?
Zero trust security assumes that the network is always hostile, which means internal and external threats exist on the network at all times. The approach is to authenticate and authorize users and devices before granting access to enterprise resources regardless of the location of those users or devices. The mantra that defines the zero-trust approach is, “never trust, always verify”.
Network security traditionally depended on a perimeter-based approach. The perimeter model segmented an enterprise network into zones and enforced security controls such as firewalls at the perimeter of each zone.
However, perimeter controls can be bypassed, and threat actors can move laterally through a network zone without any restraints once they’ve compromised a host in that zone. Furthermore, as users and assets dynamically shift location due to remote work and cloud adoption, static perimeter-based controls don’t suffice because there is no easily definable perimeter.
The zero-trust approach reflects the current threat landscape by dynamically analyzing access requests and aiming to answer three questions:
- Who has access to which data, applications, systems, and other resources?
- Who should have access to those same resources?
- What are users doing with their current levels of access?
This approach changes the focus from protecting network segments to protecting resources by not granting explicit trust based on physical or network location or asset ownership.
Zero Trust Security Principles and Examples
Three core principles drive every zero trust implementation:
- Secure Access to All Resources: this principle states that zero trust requires a holistic approach that authenticates and authorizes every access attempt on the network to any resource. The assumption is that every access request is hostile until proven otherwise.
- Adopt Least Privilege Access: least privilege access limits user access to only the resources strictly necessary for carrying out their job duties. Adopting least privilege access is imperative in reducing the attack surface in modern IT environments.
- Monitoring and Logging: from network flows to file access requests, successful zero trust security depends to a large extent on monitoring, logging, and inspecting everything on the network. This third principle, which should leverage automation, helps establish insight into baseline levels of normal activity and dynamically enforce access policies based on anomalous behavior.
Two examples of zero trust defense areas are:
Example 1: Infrastructure Protection
A zero trust model protects valuable IT infrastructure from advanced cyber threats using least privilege access, behavior-based anomaly detection, and telemetry to ensure your business doesn’t suffer a business continuity event that renders mission-critical services unavailable.
Example 2: Comprehensive Data Protection
Deploying a zero trust model can move your organization from perimeter-based data protection to contextual, access-driven protection that discovers, classifies, and protects data comprehensively across a distributed IT environment.
Benefits of Zero Trust Security
The following are some of the main benefits of using a zero trust approach to security:
- Better data breach protection—the zero trust model assumes that everything on the network is hostile and limits access privileges, which helps protect against both insider and external sources of data breaches.
- Improved visibility—effective zero trust security requires comprehensive visibility into data, users, and devices, which ultimately enables visibility into the context of every access request and a more robust cybersecurity posture across a hybrid infrastructure and remote workforce.
- Easier risk identification—the visibility driven by zero trust makes it easier to identify important information security risks, such as excessive privileged access levels or non-compliance activities.
- Improved governance—zero trust helps organizations figure out where their sensitive data is and better govern how access is provided to that data using controls such as least privilege access.
- Proactive threat detection—because zero trust inspects and logs network traffic and uses context-based dynamic access provision, it can proactively detect cyber threats by providing granular insight into suspicious network behavior.
Enforcing Zero Trust with Anomaly Detection
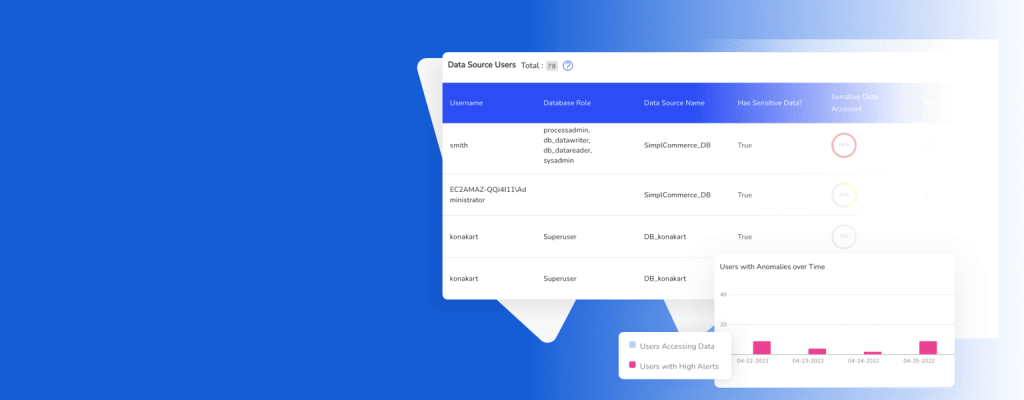
Zero trust doesn’t just happen—its implementation requires people, processes, and solutions. The ability to track data access and detect anomalies in behavior, usage patterns, and other events is critical for successfully enforcing zero trust. Anomaly detection solutions can identify events and observations that warrant suspicion and indicate possible threats to data and other resources.
Modern anomaly detection solutions aligned with a zero-trust model should use an AI-driven approach powered by machine learning algorithms. These algorithms can find outliers in data access, VPN activity, or other behavior on the network with sufficient granularity to enforce dynamic access policies and proactive threat detection.
For example, an anomaly detection system flags an employee attempting to download 10 gigabytes of information from a customer database at 2 AM from an IP address in an unexpected location. The suspicious activity is then blocked based on these contextual anomalies to prevent a data breach incident.
Anomaly detection, in turn, depends on comprehensive data visibility. Your organization needs to map and classify data in order to know:
- Where all their data resides across a complex, distributed ecosystem.
- What type of data is it? How sensitive? How critical? What are the compliance requirements on them?
- Who touches critical data, where and how, regardless of point of access or source.
Conclusion
Zero trust will continue to flourish as a pinnacle of modern cybersecurity as evidenced by its express recommendation in official US government directives and its increased business-wide adoption in the private sector. At the heart of zero trust’s effective implementation is the ability to discover and classify all of your organization’s data assets.
DruvStar Data Vision™ closes the data visibility gap in fragmented, distributed, complex environments to provide a 360-degree, comprehensive view of data and access through the entire lifecycle— enabling your business to move toward a zero-trust security environment. Learn more.