CCPA: Three Years Later
The governor of California passed the CCPA into law in June 2018, and it went into effect in January 2020. The intention behind this regulation was to strengthen privacy rights and privacy protection for residents of California.
Companies that must comply with CCPA include:
- Companies of any size that have personal data on at least 50,000 Californian residents
- Companies that collect more than half of their revenues from the sale of Californians’ personal data
- Companies that serve California residents and have at least $25 million in annual revenue
As with many data protection regulations, the CCPA carries penalties for non-compliance. Violating any aspect of the CCPA, such as failing to provide adequate notice when collecting customer data, can result in fines of:
- $7,500 per intentional violation
- $2,500 per unintentional violation
In the event of a data breach arising from CCPA violations, customers have the right to pursue civil legal claims against businesses. In fact, one such lawsuit citing CCPA resulted in a $400,000 settlement between clothing retailer Hanna Andersson and affected customers after a data breach.
CCPA Compliance: Personal Data
The CCPA uses a broad definition of personal data as “information that identifies, relates to, describes, is capable of being associated with, or could reasonably be linked, directly or indirectly, with a particular consumer or household”. In practice, examples of this information include:
- Social security numbers
- Email addresses
- Postal address
- Records of products purchased
- Fingerprints
- Driver’s license or passport scans
Proper classification of data is so important in the context of CCPA compliance because there could be gaps between what the regulation defines as personal data versus how your business defines it. Misclassifications can result in not putting sufficient controls in place to protect data, such as redacting certain types of information that could be personally linked to a particular customer. Misclassification may also result in improper disclosure to customers on the kind of personal data your organization collects about those customers.
CCPA vs GDPR: Similarities and Differences
Several governance, risk, and compliance experts and commentators refer to CCPA as the American version of the European Union’s GDPR regulation. There’s no doubt that the introduction of GDPR in 2016 followed by its effective start date in 2018 shaped and motivated the need for equivalent US legislation. California led the way in the US for data protection with the CCPA.
Both regulations have similar rules requiring businesses to disclose the categories of personal information collected about people and the intended uses for each category. Once again, the ability to do this starts with properly classifying your data. Another similarity is that both regulations can apply to businesses outside the
An interesting difference in defining personal information between CCPA and GDPR is that CCPA is broader in its definition of personal information. The definition includes information relating to both a particular consumer or “household”. In practice, this definition means you need to be extra cautious about how you classify the data you collect and understand whether CCPA rules apply to that data.
CPRA: Strengthening CCPA Compliance Requirements
Highlighting how data protection regulations often evolve and become more stringent over time is the California Privacy Rights Act (CPRA), which extends and amends the original CCPA law. CPRA comes into effect in January 2023.
Among the main changes from CPRA is a new category of data that needs protection, which has been termed sensitive personal information (SPI). This new change poses problems for companies that haven’t taken data classification seriously enough as part of their baseline compliance processes.
The definition of SPI data covers government identification, financial account information, geolocation, biometrics, health, sexual orientation, and religion. CPRA will give people the choice of limiting how their sensitive data is used or disclosed. Without a clear and precise map of the data you collect, your organization may struggle to accurately categorize sensitive personal information, which can easily lead to non-compliance.
Further increasing the data misclassification risks is that CCPA includes employees in the definition of consumers. While substantive requirements for protecting employee data with the same enforcement as consumer data won’t come into effect until the CPRA’s effective date in January 2023, compliance still requires that employers provide notice to employees at the point of data collection.
Benefits of Automated Tools for CCPA Compliance
It’s imperative if your business needs to comply with CCPA that you’re clear and precise about what sensitive data you have about customers and employees and where that data resides. Data classification ensures you properly enforce relevant controls and follow proper procedures for personal data covered by regulations like CCPA.
In the context of a complex IT ecosystem and a dynamic data environment, manually finding and classifying this data is a massive undertaking. Without the solid foundation provided by understanding where you store and who accesses sensitive regulated data across on-premise and cloud environments, your compliance efforts are likely to fall short. While spreadsheets may have sufficed in the comparatively primitive IT environments of ten years ago, this sort of manual undertaking is not practical or efficient today.
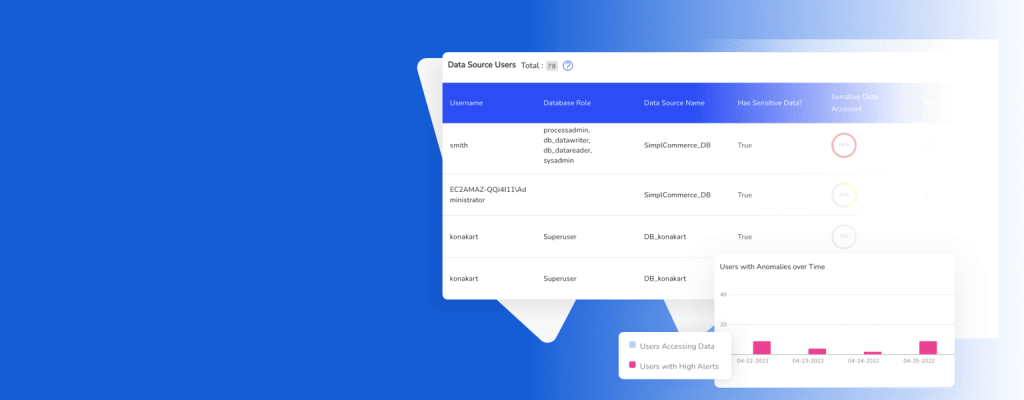
Automated tools can be a game-changer in helping to achieve compliance with CCPA and other regulations. Of specific benefit are tools that can map data to simplify its discovery and classification. Ideally, this data mapping should provide visibility into who has access to data, what format the data is in, the purpose of having the data, and what users are doing with their access. Tools leveraging pre-built connectors and APIs can effortlessly discover and help classify data in data stores and third party apps.
A good data map can provide you with a visual story of data that can help you ensure specific obligations and processes are in place that ensure compliance with CCPA. Automated data mapping tools make it easier to record processing activities, notify relevant parties in a timely and transparent manner about data collection, and properly protect all sensitive information.
Improving CCPA Compliance
If your business wants to improve CCPA compliance, the position you need to start from is comprehensive data visibility. Only from this baseline can you implement effective data governance and protect personal customer or employee data. As both IT ecosystems and the CCPA evolve, the need to close your data visibility gaps and properly classify data will only grow stronger.
Streamline and simplify your CCPA compliance by automating data discovery and classification with DruvStar Data Vision. Learn about Data Vision’s comprehensive data security mapping that can help you improve compliance with a variety of regulations.