Dangers in the digital world are growing due to an expanding army of professional attackers exploiting security weaknesses and leaving businesses vulnerable. Cybersecurity should be a top concern for business continuity – there is near certainty that your business has been attacked or will be attacked in the next 12 months. So, how should a business avoid becoming a victim?
- Firstly, companies should recognize that no easy or magical technology can solve this for them, despite claims of some vendors to the contrary.
- Secondly, they must recognize that 95% of all breaches are caused by human error. The remainder comes from weaknesses in internal and third-party systems.
- Thirdly, companies must be prepared to implement a multi-layered approach, to protect their users, systems, and data.
Avoiding becoming a victim of cybersecurity risks is an arduous task for any company, but the following are the most effective ways of lowering your cybersecurity risks:
1. Create a security plan
A security plan is the collection of practices and procedures that prevent data from being leaked or otherwise compromised. The security plan outlines the following:
- The company’s security policies
- Who should be responsible for what
- Which types of data are to be handled, stored, or transmitted
It also specifies the roles and responsibilities in case any incident occurs. There is a need to provide details on how an emergency will be managed as well. This includes information like who would contact law enforcement agencies, insurance carriers, lawyers, etc., and whether there is a plan for getting back up after anything happens (e.g., restoring databases). The foremost step towards securing your company from cybersecurity risks is having a sound security policy that outlines all liabilities concerning data protection issues that might arise due to human error or system vulnerabilities. A good place to start if you don’t already have one is with the NIST Cybersecurity Framework.
Additional Resources:
- U.S. Department of Homeland Security – “Cybersecurity and Emergency Management”
- National Institute for Standards in Technology (NIST) – “Framework for Improving Critical Infrastructure Cybersecurity”
- Federal Trade Commission’s Bureau of Consumer Protection
2. Train your users on cybersecurity concerns
In almost every successful cyber breach, the common denominator is human error. Failure to install security updates on time, weak passwords, and giving up sensitive information are all ways that human error can manifest.
According to IBM Cyber Security Intelligence Index Report, human error contributed to 95% of all breaches. Companies should provide employees with the necessary training in cyber-security to protect their businesses. They must recognize that no matter how state-of-the-art of a security system you implement there will always be vulnerabilities as long as people are around.
Implement IT training where employees are trained in the do’s and don’t’s when it comes to cybersecurity, such as how to avoid phishing schemes or scams that could compromise their credentials.
3. Know your assets and dependencies
Knowing your attack surface is essential to understanding your security risk. Know what devices are connected to the network, who has access, and how they got it.
When it comes to cybersecurity, your company shouldn’t be in the dark. Be sure to keep an eye on any new security updates that could patch vulnerabilities in your system and have one or more members of your team assigned to do so.
Every company should take inventory of its assets, which includes everything from hardware to data storage media including files on employees’ desktops and mobile devices such as laptops and smartphones.
4. Test for vulnerabilities
When trying to strengthen your organization’s information security posture, it’s natural to turn to the latest tools and technologies to help combat the latest threats. Before jumping the gun and seeking out flashy new solutions, though, you must identify existing vulnerabilities within your IT infrastructure.
Vulnerability scanning and penetration testing are two activities commonly used to identify weaknesses in servers, operating systems, application services, and network devices that attackers can exploit.
The number of vulnerabilities found in production code and recorded in the US-CERT Vulnerability Database reached a record high of 18,335 in 2020. This was the fourth year in a row that record levels of vulnerabilities were reported.
Examples of vulnerabilities include badly configured network firewalls, application logic flaws, and inadequate endpoint security. Given the number of vulnerabilities and the high costs of an information security breach, efforts to proactively find and fix network security weaknesses are fundamental in improving your cybersecurity defenses.
For example, if you have any ports open or network shares that are no longer needed, change the access permissions so they can’t be accessed by anyone but yourself. You want to make sure that there are no known errors in your exposed endpoints and applications, errors that a hacker may exploit to run a cross-site script or inject unintended data to leverage security weaknesses.
5. Monitor and manage threats
According to industry statistics, over 80% of compromises happen in minutes but, to detect that breach takes over 190 days. To contain the breach takes at least a further 60 days – that’s over 250 days from attack to containment. This time frame gives ample opportunity for the bad actors to exploit security weaknesses for stealing your precious data or taking over your systems.
Research has shown that companies that contained a breach in less than 30 days saved over $1 million when compared with those who did not perform proactive detection.
Businesses are typically attacked 100s of times every week. To stay ahead of attacks, you need the ability to stop them before they happen by proactively monitoring all your systems 24/365 using advanced in-depth detection that looks both inside as well as outside your organization’s perimeter.
Proactive detection is the only way to stay up to date on the daily attacks that your business faces. Using advanced solutions that utilize machine learning technology and risk-based prioritization, you can contain and remediate most threats before they have the chance to cause a data breach or any other costly damage.
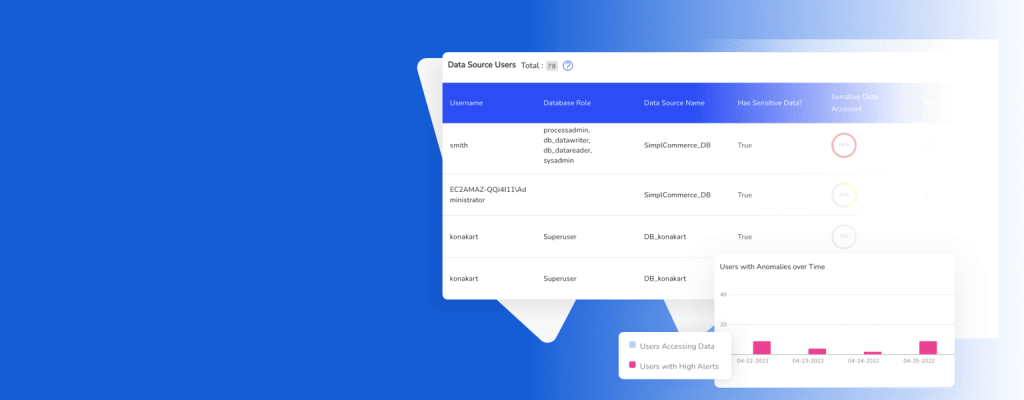
Using security tools like Security Event and Incident Monitoring (SEIM) can raise alerts about suspicious user activities or data anomalies that may be an indication of a potential attack. You can also turn to companies that offer managed detection and response (MDR) services. These provide skilled security analysts who can analyze and prioritize alerts on the company’s behalf. Additionally, they know how to act quickly to shut down an attack.
6. Respond to security incidents effectively
While prevention is the best way to protect your business from cyberattacks, effective incident response strategies can greatly reduce the impact of a breach.
Companies should have a plan in place so they know what steps need to happen when an attack is detected – this can include notification procedures, containment strategies, or post-breach response protocols.”
Effective incidence response requires automation and in-depth expertise. Services like DruvStar’s Managed Detection and Response as well as Security Incident and Event Management solutions provide industry-leading, 24×7 security incidence response.
Conclusion
Many companies feel overwhelmed at the thought of managing cybersecurity themselves. Many small to mid-sized companies fail to invest in cybersecurity because they do not understand it. 65% of all cyberattacks target small to mid-sized companies, and therefore ignoring cybersecurity could prove costly.
Running an SMB is challenging, time-consuming, and stressful, but a business should never neglect cybersecurity. If you don’t have an in-house security team and a large IT budget, then you can turn to Managed Detection and Response services like DruvStar which specializes in helping businesses improve their security posture at affordable prices.
DruvStar’s unique approach is designed to protect a business’ users, data, and systems, which is accomplished by concentrating on major risk areas. DruvStar B2B solutions enable clients to implement security assurance rapidly within 3-4 weeks, lowering their risk and helping meet compliance requirements at affordable prices. There is absolutely no reason to risk your business.
Contact us today if you’d like our help to improve your company’s security posture.